IDOR Explained: How Insecure Direct Object Reference Breaks Your Authorization
One of the Most Dangerous Authorization Mistakes Developers Still Make
🤖 Curious AI enthusiast and Software Engineer with 7+ years of experience. 🛠️ I enjoy getting my hands dirty with new technologies — experimenting, building side projects, and learning by doing. 🚀 Currently exploring how AI can enhance real-world web applications.
🚨 Introduction
You can build beautiful APIs.
You can have authentication.
You can even have JWTs, OAuth, and encrypted traffic.
And still ship a critical vulnerability.
That vulnerability is IDOR — Insecure Direct Object Reference.
It’s simple.
It’s common.
And it’s responsible for some of the most serious real-world data leaks.
Let’s break it down properly — what it is, how it happens, how attackers exploit it, and how modern teams prevent it in 2026.
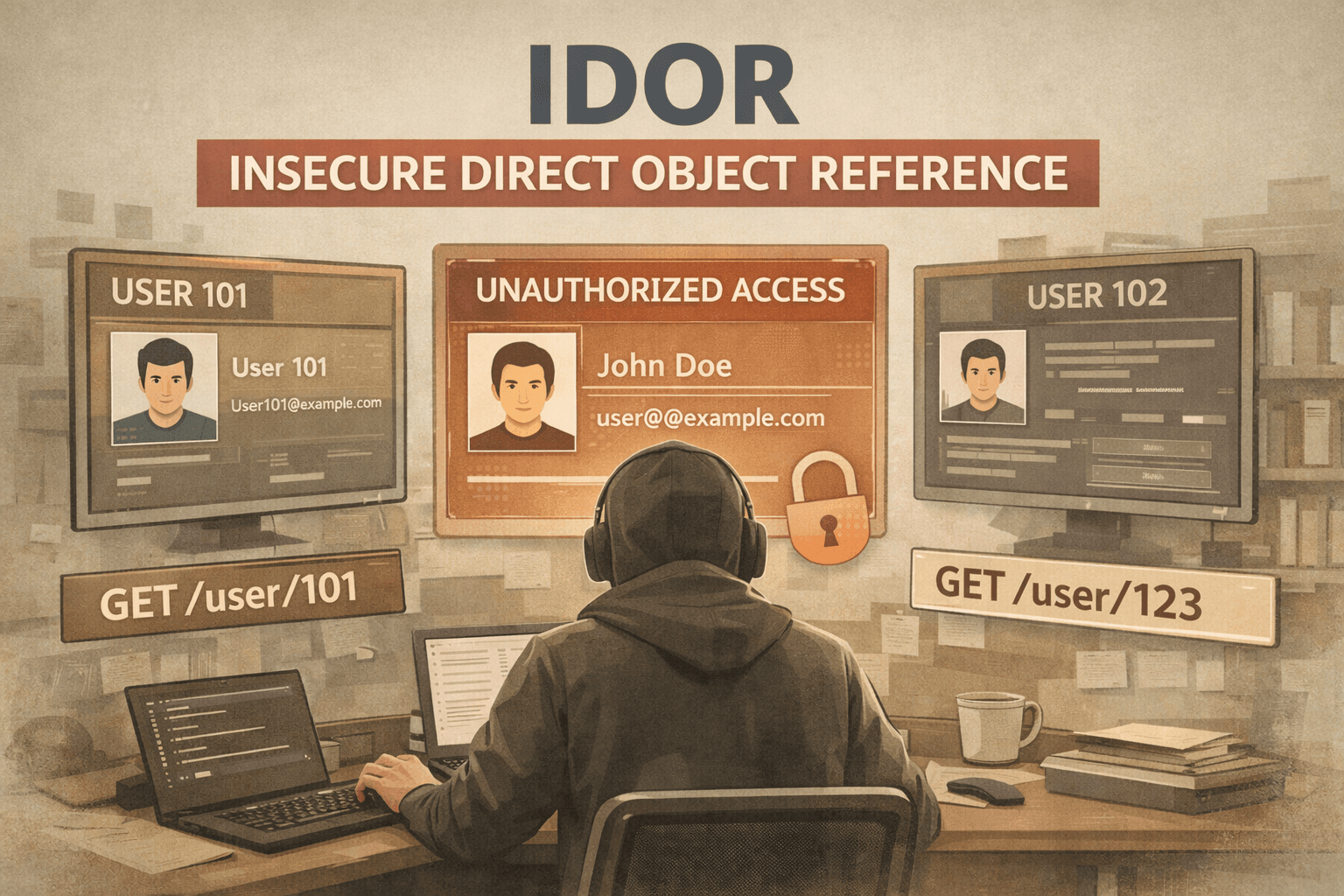
🧠 What Is IDOR?
IDOR (Insecure Direct Object Reference) occurs when an application exposes a direct reference to an internal object (like a database ID) without properly checking whether the user is authorized to access it.
In simple terms:
The system verifies who you are — but not what you’re allowed to access.
That’s an authorization failure.
And in modern security standards, this falls under:
Broken Access Control (OWASP Top 10)
💥 The Classic Example
Let’s say your API has this route:
GET /api/users/123
Backend code:
app.get('/api/users/:id', async (req, res) => {
const user = await User.findById(req.params.id)
res.json(user)
})
Now imagine:
You are logged in as user ID 101
You change the request to:
GET /api/users/102
If the server does not verify ownership, you now have access to another user's data.
No hacking tools required.
No brute force.
Just changing a number.
That’s IDOR.
🔥 Why It’s So Dangerous
With IDOR, attackers can:
View other users’ personal data
Download invoices
Access private files
Modify someone else’s account
Delete resources they don’t own
It’s not a theoretical issue.
It’s one of the most exploited vulnerabilities in production systems.
🧩 Where IDOR Commonly Appears
IDOR doesn’t just happen in user profiles.
It often shows up in:
📦 Orders
GET /orders/98765
📄 Documents
GET /documents/abc123
🧾 Invoices
GET /invoice/4455
📁 File Downloads
GET /files/report.pdf
If access control isn’t enforced properly, all of these can be exposed.
⚠️ Authentication ≠ Authorization
This is the mistake many developers make.
Authentication → Who are you?
Authorization → What are you allowed to access?
IDOR happens when authentication exists but authorization checks are missing or incomplete.
🛠️ The Correct Way to Fix It
❌ Wrong Approach
const order = await Order.findById(req.params.id)
✅ Correct Approach
const order = await Order.findOne({
_id: req.params.id,
userId: req.user.id
})
Now the query ensures:
The order exists
It belongs to the logged-in user
This simple pattern eliminates most IDOR cases.
🔐 Best Practices to Prevent IDOR (2026 Standard)
Modern engineering teams follow these rules:
1️⃣ Always Scope Database Queries by Ownership
Every resource should be tied to:
userId
organizationId
role
permission policy
Never fetch by ID alone.
2️⃣ Centralize Authorization Logic
Instead of scattering checks everywhere:
Use:
Middleware
Policy layers
Access control services
For example:
if (!canAccess(req.user, resource)) {
return res.status(403).json({ error: "Forbidden" })
}
Centralizing reduces human error.
3️⃣ Use Role-Based or Attribute-Based Access Control
Modern systems use:
RBAC (Role-Based Access Control)
ABAC (Attribute-Based Access Control)
This makes permission decisions consistent and scalable.
4️⃣ Avoid Predictable IDs (Optional but Helpful)
Sequential IDs:
/user/1
/user/2
/user/3
Very easy to enumerate.
Better:
/user/550e8400-e29b-41d4-a716-446655440000
UUIDs reduce guessing — but they do NOT replace proper authorization checks.
5️⃣ Log Suspicious Access Patterns
If a user tries:
/user/100
/user/101
/user/102
/user/103
That’s enumeration behavior.
Modern systems log and alert on this.
🧪 How to Test Your App for IDOR
Here’s a simple developer checklist:
Log in as User A
Capture a request like:
GET /api/orders/123Change the ID to another value
Replay the request
If you get valid data → you have an IDOR vulnerability.
Security engineers test this constantly.
🏗️ How Modern Teams Design Against IDOR
In mature systems, you’ll see:
Object queries always scoped to ownership
Middleware handling authorization
Centralized permission services
Automated security tests in CI
API contracts enforcing access rules
Security reviews during PR
Security is built into the architecture — not patched afterward.
📌 Real-World Example (Multi-Tenant SaaS)
Imagine a SaaS dashboard:
GET /api/projects/abc123
Correct query:
const project = await Project.findOne({
id: req.params.id,
organizationId: req.user.organizationId
})
This prevents users from accessing projects outside their organization.
This is how serious SaaS platforms avoid cross-tenant data leaks.
🧠 Why IDOR Is Still So Common
Because it’s easy to overlook.
Developers think:
“The user is logged in.”
“The UI hides the button.”
“Nobody will try changing the ID.”
Attackers absolutely will.
🎯 Key Takeaways
IDOR is an authorization failure.
It allows users to access resources they don’t own.
It’s part of OWASP’s Broken Access Control category.
Fixing it requires proper ownership checks in every query.
Modern systems centralize and automate authorization.
🚀 Final Thoughts
IDOR is dangerous because it’s simple.
No SQL injection.
No complex exploit chains.
Just changing a number in a request.
In 2026, secure development isn’t optional.
Authorization logic is core infrastructure.
If you build APIs, SaaS products, dashboards, or file systems —
you must treat access control as seriously as authentication.